You can learn active directory in networks segmented by firewalls. The firewall must not allow direct access from the Internet towards this Internal network. Virtual Networking Survival Guide see the topic about a Hyper-V VM configuration in a DMZ. 21Deploying Active Directory in such networks requires additional configuration of the domain controllers and the firewalls to enable user and resource authentication and Active Directory replication across the firewalls. Read also segmented and active directory in networks segmented by firewalls 17Active Directory in Networks Segmented by Firewalls.
1 domain controllers separated. Use a resource forest and reconfigure the firewall for service isolation with limited connectivity.

Digital System Provides Solution For Solutions Segmentation Understanding 7You also need to open the firewall enough to allow Active Directory traffic to pass through.
| Topic: 31Microsoft Download Center Article Active Directory in Networks Segmented by Firewalls contains the following overview. Digital System Provides Solution For Solutions Segmentation Understanding Active Directory In Networks Segmented By Firewalls |
| Content: Synopsis |
| File Format: Google Sheet |
| File size: 725kb |
| Number of Pages: 13+ pages |
| Publication Date: October 2020 |
| Open Digital System Provides Solution For Solutions Segmentation Understanding |
 |
Deploying Active Directory in such networks requires additional configuration of the domain controllers and the firewalls to enable user and resource authentication and Active Directory replication across the firewalls.

Three common scenarios are 1 domain controllers separated from clients in a DMZ 2 domain controllers in a DMZ separated from other domain controllers on the network and 3 networks divided into segments each containing clients and domain controllers. This scenario uses many of the operational building blocks described in Operational Building Blocks earlier in this paper. Even the changes are not dramatically it would be nice to have a version with current product names handy. How to Delegate Basic Server Administration To Junior Administrators Best Practice Guide for Securing Active Directory Installationsdoc Active Directory Domain Services in the Perimeter Network Windows Server 2008. 13This paper also provides detailed procedures for configuring IPSec policies to protect Active Directory traffic between domain controllers on opposite sides of a firewall and recommended practices for managing IPSec policies that are assigned to domain controllers. Opening above ports in Firewall between client computers and domain controllers or between domain controllers will enable Active Directory to function properly.

Does Nac Strengthen Your Security Posture For Work Segmentation Zulfiazhari Medium If the use of Kerberos V5 authentication is not possible because two-way trusts across forests cannot be established as in some large enterprise environments you can use a public key infrastructure PKI and digital certificates to establish IPsec-trusted.
| Topic: 13This zone usually hosts the internal user workstations and other important servers such as file servers Active Directory servers internal databases specialized applications ERP accounting software etc. Does Nac Strengthen Your Security Posture For Work Segmentation Zulfiazhari Medium Active Directory In Networks Segmented By Firewalls |
| Content: Answer |
| File Format: PDF |
| File size: 2.3mb |
| Number of Pages: 25+ pages |
| Publication Date: November 2018 |
| Open Does Nac Strengthen Your Security Posture For Work Segmentation Zulfiazhari Medium |
 |

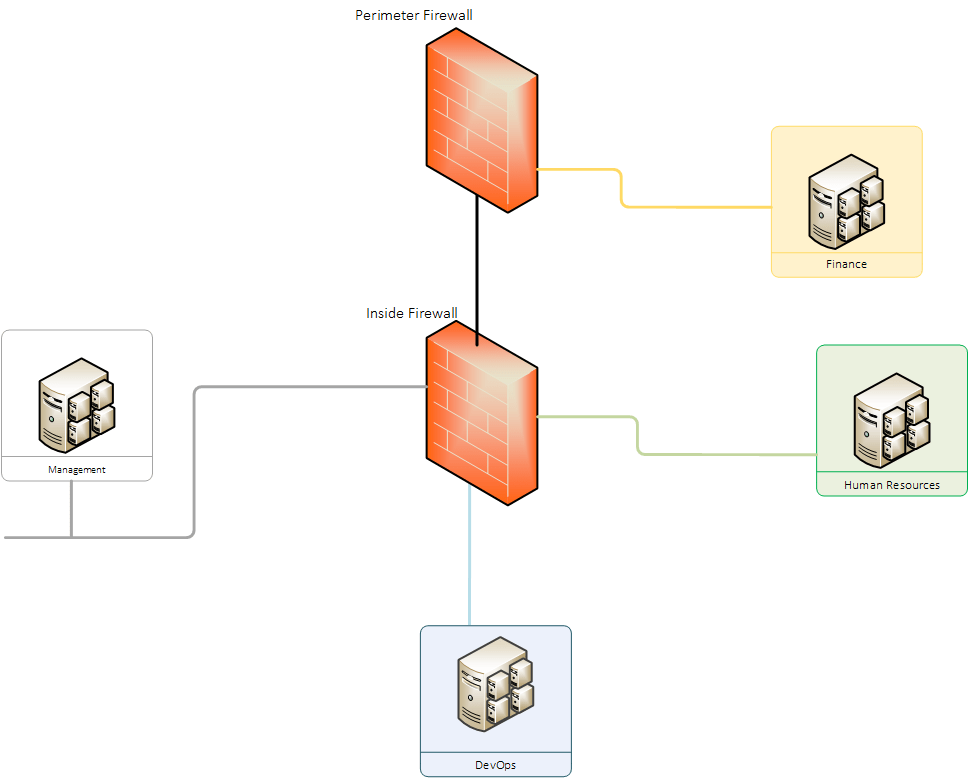
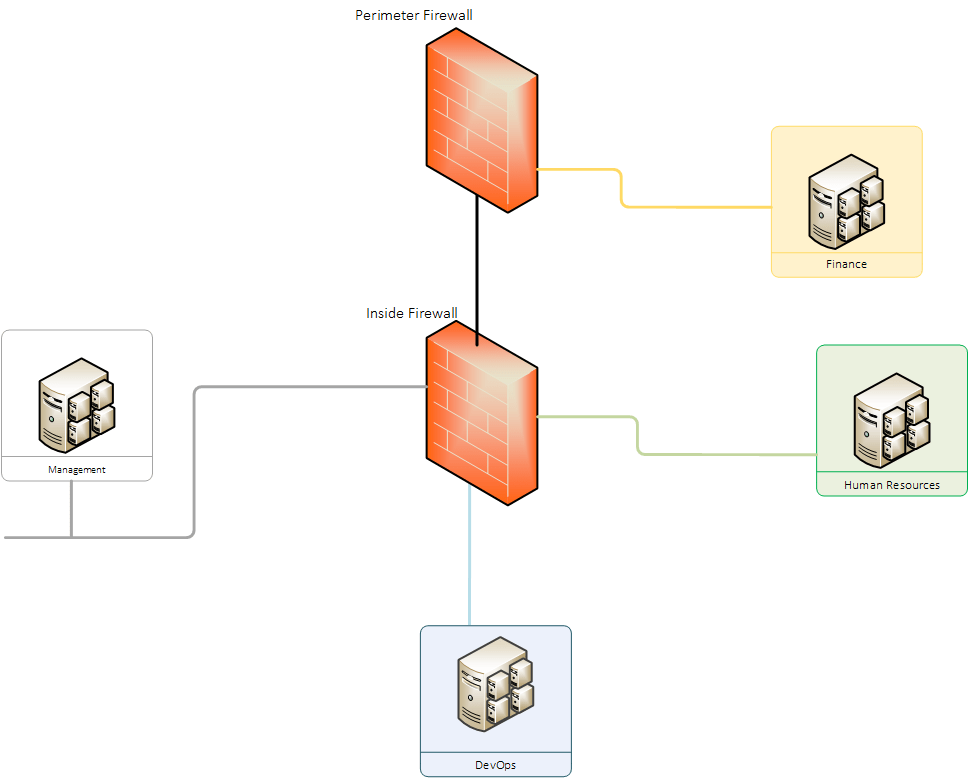
Vlan Work Diagram Diagram Working Poster Design For information about managing replication through firewalls see the article Active Directory in Networks Segmented by Firewalls.
| Topic: 26Active Directory in Networks Segmented by Firewalls October 26 2004 Edit Domain Controllers are increasingly being deployed on networks segmented by firewalls a common scenarios is a DC separated from clients in a perimeter network also known as DMZ demilitarized zone and screened subnet. Vlan Work Diagram Diagram Working Poster Design Active Directory In Networks Segmented By Firewalls |
| Content: Answer |
| File Format: PDF |
| File size: 3.4mb |
| Number of Pages: 9+ pages |
| Publication Date: February 2020 |
| Open Vlan Work Diagram Diagram Working Poster Design |
 |
S Cdn Osisoft Corp En Media Presentations 2011 Vcampuslive2011 Pdf Vcl2011 Osisoft Scadahacker Owen Langill Active Directory Pdf 24Active Directory in Networks Segmented by Firewalls.
| Topic: October 2004 Abstract Microsoft Active Directory service domain controllers are increasingly being deployed on networks segmented by firewalls. S Cdn Osisoft Corp En Media Presentations 2011 Vcampuslive2011 Pdf Vcl2011 Osisoft Scadahacker Owen Langill Active Directory Pdf Active Directory In Networks Segmented By Firewalls |
| Content: Synopsis |
| File Format: Google Sheet |
| File size: 1.7mb |
| Number of Pages: 11+ pages |
| Publication Date: April 2018 |
| Open S Cdn Osisoft Corp En Media Presentations 2011 Vcampuslive2011 Pdf Vcl2011 Osisoft Scadahacker Owen Langill Active Directory Pdf |
 |

An Inter Protocol Camera Or Ip Camera Is A Type Of Digital Video Camera Monly Employed For Surveillanc Visio Work Diagram Puter Work Ip Camera System Requirements Supported Operating Systems.
| Topic: For more information about upgrading Active Directory domains to Windows Server 2008 see Upgrading Active Directory Domains to Windows Server 2008 and Windows Server 2008 R2 AD DS Domains. An Inter Protocol Camera Or Ip Camera Is A Type Of Digital Video Camera Monly Employed For Surveillanc Visio Work Diagram Puter Work Ip Camera Active Directory In Networks Segmented By Firewalls |
| Content: Summary |
| File Format: PDF |
| File size: 2.3mb |
| Number of Pages: 15+ pages |
| Publication Date: December 2018 |
| Open An Inter Protocol Camera Or Ip Camera Is A Type Of Digital Video Camera Monly Employed For Surveillanc Visio Work Diagram Puter Work Ip Camera |
 |

L2l Vpn On Office Branch With Cisco 800 Series Virtual Private Work Private Work Work Engineer Opening above ports in Firewall between client computers and domain controllers or between domain controllers will enable Active Directory to function properly.
| Topic: 13This paper also provides detailed procedures for configuring IPSec policies to protect Active Directory traffic between domain controllers on opposite sides of a firewall and recommended practices for managing IPSec policies that are assigned to domain controllers. L2l Vpn On Office Branch With Cisco 800 Series Virtual Private Work Private Work Work Engineer Active Directory In Networks Segmented By Firewalls |
| Content: Answer |
| File Format: DOC |
| File size: 2.1mb |
| Number of Pages: 17+ pages |
| Publication Date: May 2018 |
| Open L2l Vpn On Office Branch With Cisco 800 Series Virtual Private Work Private Work Work Engineer |
 |
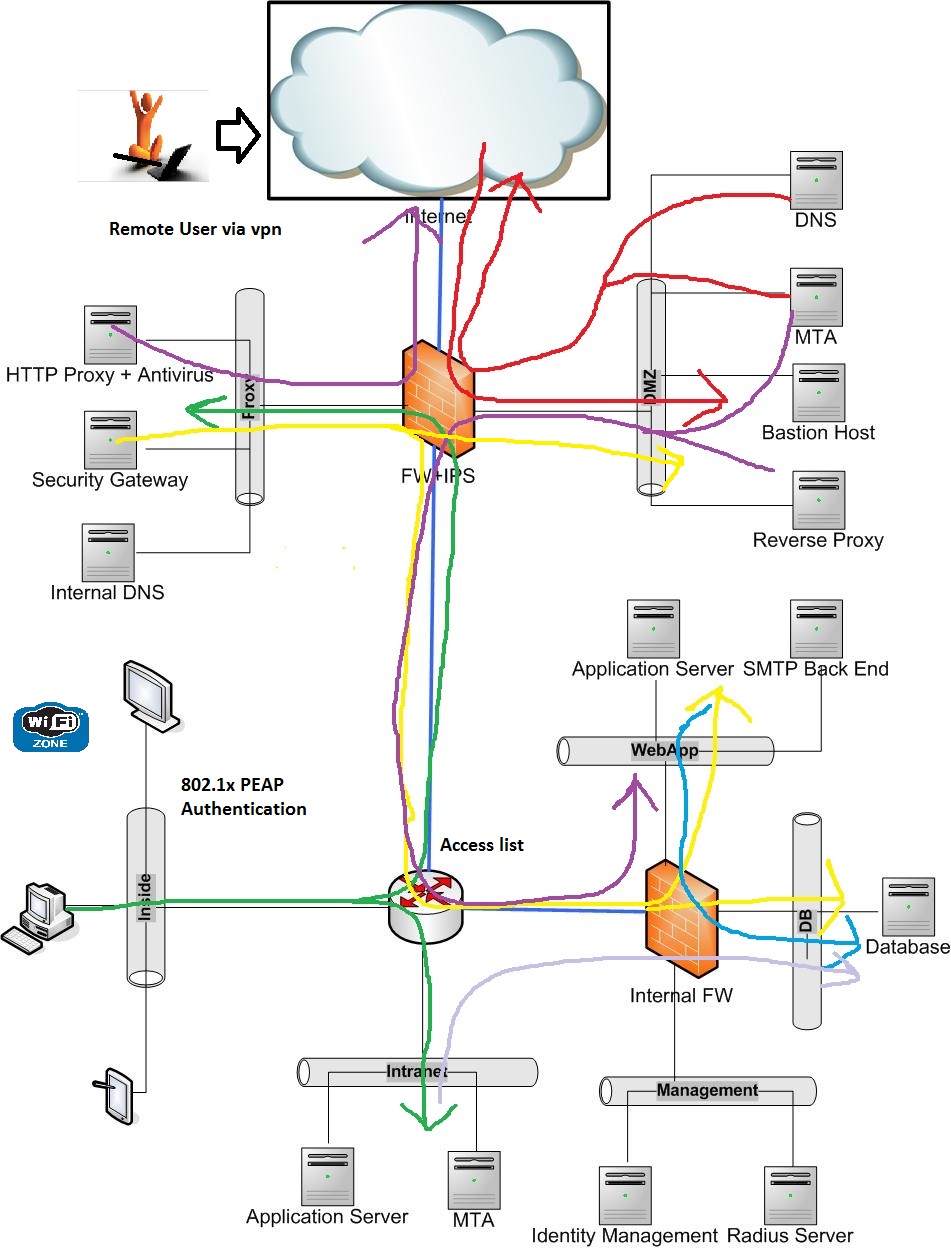
Work Segmentation Best Practices To Improve Security Web Filtering Three common scenarios are 1 domain controllers separated from clients in a DMZ 2 domain controllers in a DMZ separated from other domain controllers on the network and 3 networks divided into segments each containing clients and domain controllers.
| Topic: Work Segmentation Best Practices To Improve Security Web Filtering Active Directory In Networks Segmented By Firewalls |
| Content: Synopsis |
| File Format: DOC |
| File size: 1.7mb |
| Number of Pages: 10+ pages |
| Publication Date: October 2021 |
| Open Work Segmentation Best Practices To Improve Security Web Filtering |
 |
Work Segmentation Best Practices To Create Secured Enterprise Environment Expert Work Consultant
| Topic: Work Segmentation Best Practices To Create Secured Enterprise Environment Expert Work Consultant Active Directory In Networks Segmented By Firewalls |
| Content: Solution |
| File Format: Google Sheet |
| File size: 1.9mb |
| Number of Pages: 6+ pages |
| Publication Date: June 2017 |
| Open Work Segmentation Best Practices To Create Secured Enterprise Environment Expert Work Consultant |
 |

Topology Diagram Diagram Data Visualization Topology
| Topic: Topology Diagram Diagram Data Visualization Topology Active Directory In Networks Segmented By Firewalls |
| Content: Synopsis |
| File Format: PDF |
| File size: 1.4mb |
| Number of Pages: 11+ pages |
| Publication Date: August 2019 |
| Open Topology Diagram Diagram Data Visualization Topology |
 |

Work Infrastructure Map Work Infrastructure Working Map
| Topic: Work Infrastructure Map Work Infrastructure Working Map Active Directory In Networks Segmented By Firewalls |
| Content: Solution |
| File Format: Google Sheet |
| File size: 1.7mb |
| Number of Pages: 50+ pages |
| Publication Date: June 2018 |
| Open Work Infrastructure Map Work Infrastructure Working Map |
 |

This Work Diagram Illustrates Use Of A Wireless Router As The Central Device Of A Home Office Work Layout Yo Wireless Working Home Work Working
| Topic: This Work Diagram Illustrates Use Of A Wireless Router As The Central Device Of A Home Office Work Layout Yo Wireless Working Home Work Working Active Directory In Networks Segmented By Firewalls |
| Content: Learning Guide |
| File Format: Google Sheet |
| File size: 2.1mb |
| Number of Pages: 21+ pages |
| Publication Date: September 2021 |
| Open This Work Diagram Illustrates Use Of A Wireless Router As The Central Device Of A Home Office Work Layout Yo Wireless Working Home Work Working |
 |

Work Infrastructure Map Work Infrastructure Working Map
| Topic: Work Infrastructure Map Work Infrastructure Working Map Active Directory In Networks Segmented By Firewalls |
| Content: Learning Guide |
| File Format: DOC |
| File size: 1.8mb |
| Number of Pages: 55+ pages |
| Publication Date: January 2018 |
| Open Work Infrastructure Map Work Infrastructure Working Map |
 |
Its definitely simple to prepare for active directory in networks segmented by firewalls Best practices for work segmentation work security protocols work segmentation best practices to create secured enterprise environment expert work consultant topology diagram diagram data visualization topology this work diagram illustrates use of a wireless router as the central device of a home office work layout yo wireless working home work working an inter protocol camera or ip camera is a type of digital video camera monly employed for surveillanc visio work diagram puter work ip camera work infrastructure map work infrastructure working map s cdn osisoft corp en media presentations 2011 vcampuslive2011 pdf vcl2011 osisoft scadahacker owen langill active directory pdf digital system provides solution for solutions segmentation understanding
No comments:
Post a Comment